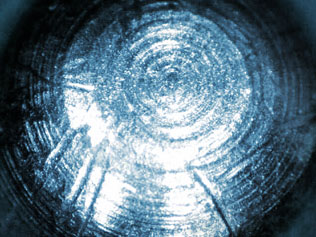
 The reason that covert intrusions are often a great cause for concern is that distinct evidence of a break-in may be unavailable. Surreptitious attacks often leave little in the way of evidence. However, even the most careful attempt at lockpicking will leave evidence within the lock itself. This evidence, if properly preserved and accurately collected and documented, can be invaluable during court proceedings should litigation become necessary.
The reason that covert intrusions are often a great cause for concern is that distinct evidence of a break-in may be unavailable. Surreptitious attacks often leave little in the way of evidence. However, even the most careful attempt at lockpicking will leave evidence within the lock itself. This evidence, if properly preserved and accurately collected and documented, can be invaluable during court proceedings should litigation become necessary.
If you have suspicion that an attempt at lockpicking, key impressioning, or other such attacks has occurred at your facility, reach out to us for help.
If you suspect that any of your security hardware has been physically tampered with or that attempts at entry (whether successful or not) have taken place, please contact the CORE Group before removing or transporting it. We can instruct you on how to preserve the scene, keep a proper chain of custody on any evidence, and submit it to us for analysis and documentation if that is your desired course of action.

 Forensics
Forensics